
Три недели назад операторы многофункционального стиллера Raccoon, пользовавшегося большим спросом у киберкриминального андерграунда, объявили о закрытии проекта в связи с гибелью на Украине одного из ключевых участников группы. Судя по заявлению операторов о невозможности поддержания и выпуска стабильных версий малвари, жертвой драматических политических событий стал основной разработчик программного кода.
Последнюю активность стиллера мы наблюдали 23 марта 2022 года, после чего операторы Raccoon, по всей видимости, отключили управляющую инфраструктуру и закрыли сервис, что отчетливо видно на наших радарах.
Впервые малварь вышла в продакшн в апреле 2019 года и c тех пор сдавалась в аренду по бизнес-модели «MaaS» («Malware-as-a-Service»), предоставляя покупателям готовую управляющую инфраструктуру и обширный функционал по краже данных:
- банковских карт
- криптовалютных кошельков
- веб-браузеров (cookie и пароли)
- электронной почты
- аккаунтов Steam
- аккаунтов Telegram
- FTP-клиентов
Кроме того, Raccoon был наделен функциями загрузки иных вредоносных модулей и выполнения PowerShell-скриптов, что позволяло использовать закриптованный стиллер в качестве инструмента первоначального проникновения и закрепления в атакуемой системе.
Накануне закрытия проекта операторы анонсировали уникальную на тот момент возможность использования Telegram-каналов в качестве C&C-серверов, что многократно повышало возможности стиллера избегать детектирования защитными решениями и его привлекательность среди аналогичных конкурентов.
Внушительный функционал, регулярные обновления и круглосуточная поддержка объясняют результаты нашего анализа, согласно которым Raccoon использовался даже такими киберкриминальными группами, как EvilCorp (ServHelper), Emotet и QakBot.
Но все же наиболее частыми соседями стиллера на пейлоад-инфраструктуре были его основные конкуренты по цеху - стиллеры RedLine и Arkei. Очевидно, подобный арсенал «в одной коробке» позволял атакующим достигать максимальных шансов на проникновение и закрепление в системах путем комбинирования вредоносных модулей.
Следуя стандартным геополитическим табу киберкрайма, операторы Raccoon, очевидно, выходцы из стран постсоветского пространства, запрещали своим клиентам использовать стиллер в отношении инфраструктуры компаний - резидентов стран СНГ. Недобросовестных покупателей малвари карали мгновенным исключением из партнерской программы без возможности манибека.
Действительно, в собранных нашей системой данных нам не удалось обнаружить признаков присутствия стиллера в информационных системах стран бывшего СССР, но удалось идентифицировать внушительный перечень атакованных компаний и учреждений в иных странах, в числе которых:
авиакомпания в Исландии
криптовалютная биржа в США
горнолыжный курорт в Канаде
строительная компания в Великобритании
строительная компания во Франции
разработчики мобильных игр и приложений в США
производитель бытовой техники в Китае
сеть парфюмерных магазинов в США
рекламное агенство в Турции
рекламное агенство в Испании
сеть ресторанов в Индии
отель в Индии
автодилер в Германии
университет в Германии
Однако строгие правила не мешали клиентам Raccoon в качестве пейлоад-инфраструктуры использовать сервера и домены, расположенные и зарегистрированные на территории России. В число стран-лидеров по масштабу инфраструктуры, использовавшейся для доставки сэмплов Raccoon, наряду с Россией вошли США, Германия, Нидерланды и Турция, неожиданно занявшая 3 место в данном антирейтинге из-за целой сети bulletproof-файлообменников.
Среди используемых TLD-зон обошлось без сюрпризов. 18% от общего количества Raccoon-доменов зарегистрированы в популярных у киберкрайма доменных зонах XYZ и TOP. Неожиданным было лишь обнаружить, что 3% выявленных пейлоад-доменов стиллера зарегистрированы в TLD-зоне Уганды. Однако факт их делегирования 1 общему серверу, расположенному на Сейшельских Островах, говорит о целенаправленной вредоносной кампании, вероятно, проводившейся одним из клиентов Raccoon летом-осенью 2021 года в отношении жителей африканской страны.
В подавляющем большинстве выявленных нами случаев сэмплы Raccoon-стиллера распространялись в виде закриптованных исполняемых файлов и лишь в единичных случаях наблюдались попытки киберпреступников использовать стеганографию для сокрытия вредоносной нагрузки в файлах изображений.
Для хранения вредоносных сэмплов в 53% выявленных случаев клиенты Raccoon-сервиса использовали арендованные частные выделенные серверы. Однако лишь 16% из них были делегированы доменные имена для проведения усиленных социальной инженерией целенаправленных фишинговых атак, в большинстве случаев связанных с распространением стиллера под видом бесплатного программного обеспечения.
В остальных 47% случаев хакеры использовали заочно доверенные для защитных решений площадки, отдавая предпочтение популярным файлообменникам. Технически более сложные и затратные варианты распространения стиллера через скомпрометированные легитимные Интернет-ресурсы по технологии «Watering Hole» единичны. Не остался без внимания и популярный в настоящее время способ распространения малвари через Discord-каналы.
В связи с гибелью главного разработчика стиллера ожидать возобновления работы Raccoon-сервиса в ближайшее время не стоит. Более того, вероятное проживание основных операторов стиллера на территории Украины ставит группу в зависимость от внешнеполитической ситуации и смещает акценты в сторону примитивных физиологических потребностей.
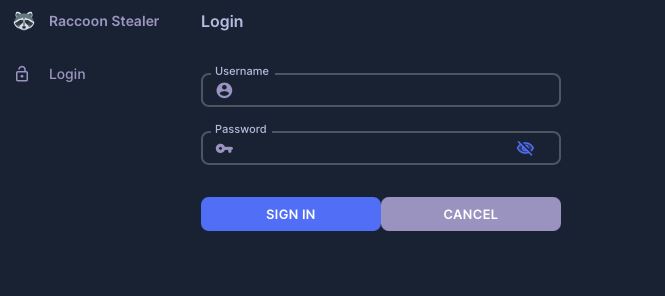
Однако несмотря на заявление о закрытии сервиса партнерская панель регистрации Raccoon продолжает функционировать, официальные аккаунты группы на киберкриминальных форумах не заблокированы. Telegram-аккаунты 3 основных операторов стиллера также подают признаки жизни. Поэтому нельзя исключать появление популярного стиллера на наших радарах в будущем.
Ну а пока продолжаем наблюдать, как рынок стиллеров захватывают конкуренты Raccoon - RedLine и Arkei.
 Raccoon. Черная полоса в жизни стиллера
Raccoon. Черная полоса в жизни стиллера